Free resource · Audit manual
Operational AI Security guide for LLMs.
The method we apply in audits and AI Security testing, opened up. Architecture risk matrix, maturity scorecard and technical fiches with recipes and regulatory mapping. Built on top of OWASP LLM Top 10 2025, designed for CTOs, security teams and compliance with LLMs in production.
What you get
An operational manual in 21 pages
Built to let a team audit an LLM system in an afternoon: prioritise by architecture, score programme maturity, apply concrete mitigations with code and check fit against the AI Act, GDPR and the Spanish framework.
LLM01 · Prompt Injection
Adversarial instructions that override the model's behaviour.
LLM02 · Sensitive Information Disclosure
PII, secrets or cross-tenant context leaking through outputs.
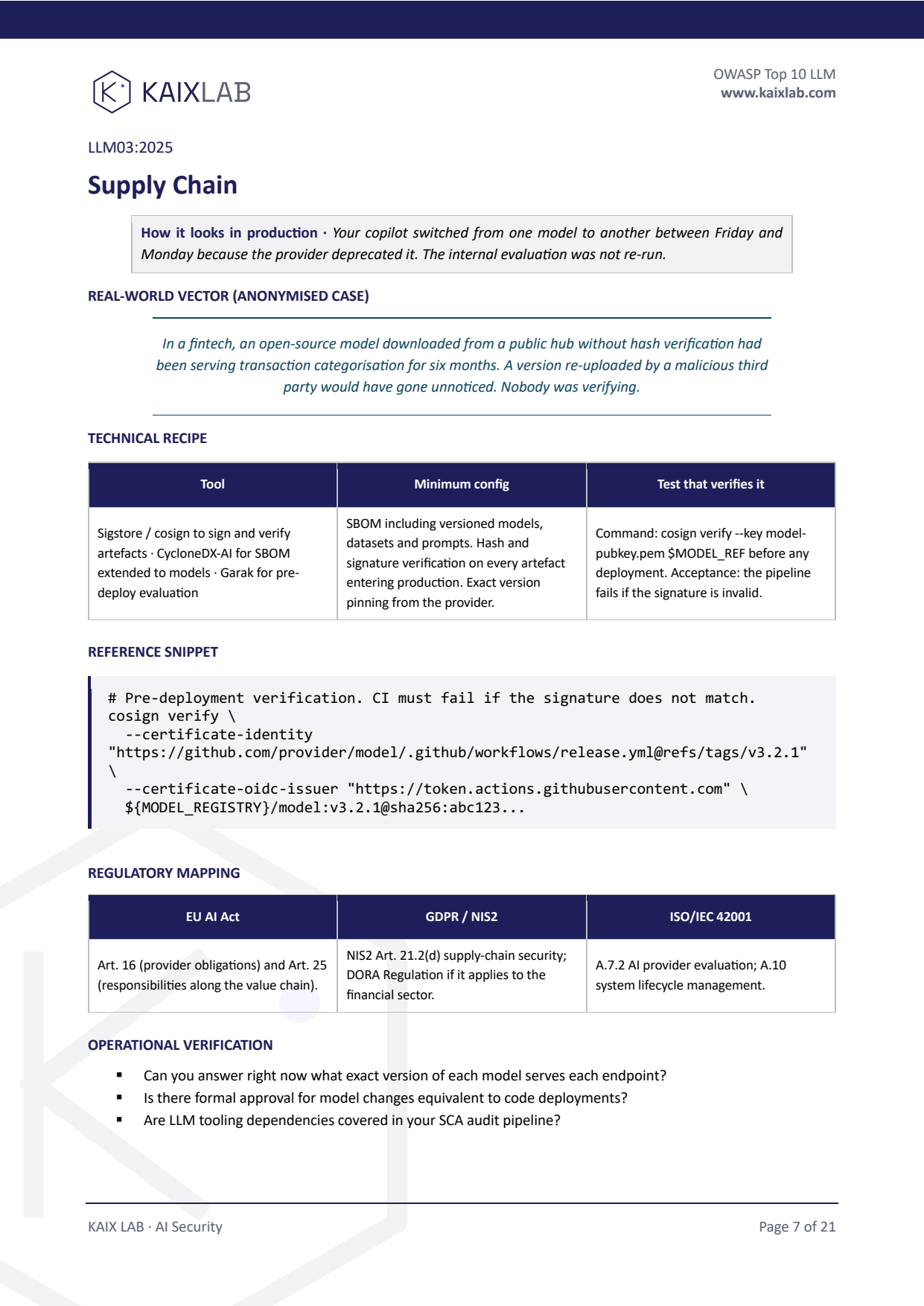
LLM03 · Supply Chain
Models, datasets and plugins of unverified provenance.
LLM04 · Data and Model Poisoning
Tampered training or fine-tuning data.
LLM05 · Improper Output Handling
LLM output executed downstream without sanitisation.
LLM06 · Excessive Agency
Agents with badly scoped permissions, tools and autonomy.
LLM07 · System Prompt Leakage
System instructions or embedded keys exposed to users.
LLM08 · Vector and Embedding Weaknesses
Vector store access, cross-tenant leakage, indirect injection via retrieved content.
LLM09 · Misinformation
Plausible-but-false answers reaching users without verification.
LLM10 · Unbounded Consumption
Cost and latency without limits: abuse, economic denial, runaway agents.
Preview
What you'll receive
Operational manual in PDF, ready for a team to apply against their own system without consulting.
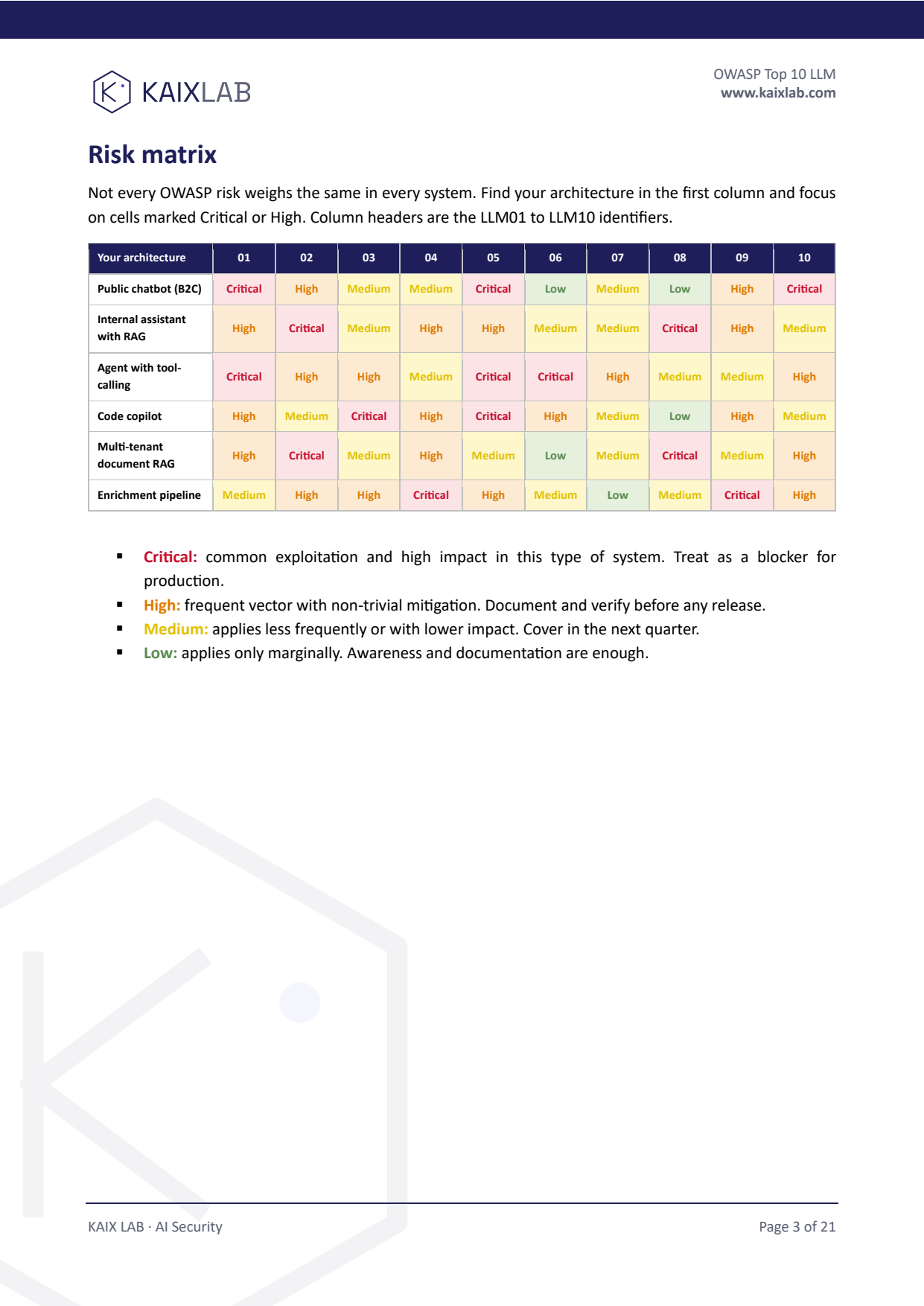
Architecture risk matrix
6 system types (public B2C chatbot, internal RAG, agent with tool-calling…) crossed with the 10 risks. Find yours and know what to prioritise.
Maturity scorecard 0-30
10 auditable controls, 0-3 score each. Three readings (high risk / partial / established programme) with associated action plan.
Technical fiches per risk (LLM01-10)
Anonymised real case, concrete tools (Garak, Lakera, Presidio, Sigstore…), minimum config, code snippets and operational verification.
Regulatory mapping
Each risk crossed with EU AI Act, GDPR, NIS2 and ISO/IEC 42001. Plus a dedicated page on the Spanish framework (AEPD, AESIA, CCN-CERT, ENS).
FAQ
Frequently asked questions
Do I have to give my email to get the checklist?
Yes, in this case you do. The OWASP LLM checklist is delivered by email. The form only asks for name, email and optional company. Privacy consent is required.
What is the checklist based on?
On the OWASP Top 10 for LLM applications. Each of the ten risks (LLM01 Prompt Injection through LLM10 Unbounded Consumption) is translated into binary checks an engineering team can apply against their own system in under one hour. Each risk has an anti-pattern observed in production and the question a real attacker would ask.
Is it only for systems already in production?
No. It also works for systems about to launch, advanced prototypes, or internal audits. The only requirement is that there is a concrete architecture to evaluate.
What happens after I download it?
You receive the PDF in your inbox. If after reading it you want us to walk the checks against your specific system, we run a free diagnostic — just reply to the email.